Tag: cdk-nag
4 posts found
Showing 4 of 4 posts


•11 min read
Use a customized CDK bootstrap template
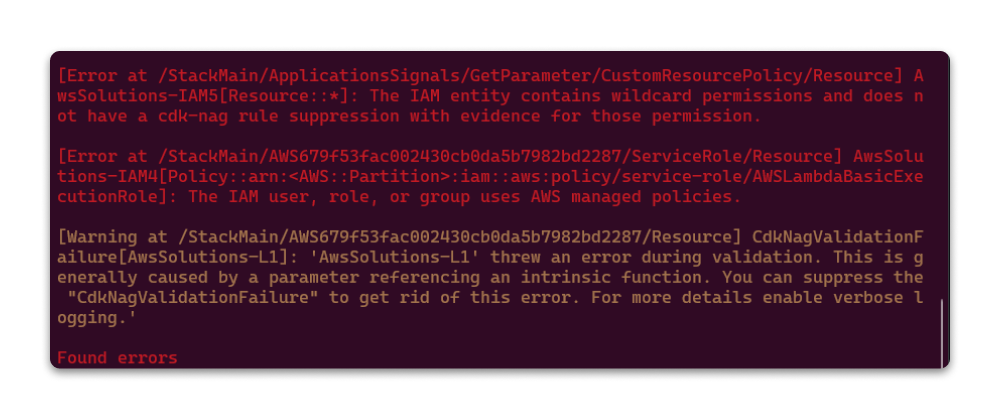
Learn how to customize the AWS CDK bootstrap template to add server access logging and KMS encryption to the staging bucket. Use the CDK Toolkit library to orchestrate multi-region deployments, extract environments from CDK apps, and validate CloudFormation templates with cdk-nag.